Backtrack 5 Wpa2 Crack Tutorial Pdf
Oct 01, 2013 WPA & WPA2 cracking with BackTrack 5 R3 New Video Exploiting Windows 10 MSFvenom & Msfconsole Backdoor Shell.
- Willis Johns
- 2 years ago
- Views:
Transcription
1 Tutorial: How to Crack WPA/WPA2 Version: 1.20 March 07, 2010 By: darkaudax Introduction This tutorial walks you through cracking WPA/WPA2 networks which use pre-shared keys. I recommend you do some background reading to better understand what WPA/WPA2 is. The Wiki [ links page has a WPA/WPA2 section. The best document describing WPA is Wi-Fi Security - WEP, WPA and WPA2 [ This is the link [ /articles/hakin9_wifi/hakin9_wifi_en.pdf] to download the PDF directly. The WPA Packet Capture Explained tutorial is a companion to this tutorial. WPA/WPA2 supports many types of authentication beyond pre-shared keys. aircrack-ng can ONLY crack pre-shared keys. So make sure airodump-ng shows the network as having the authentication type of PSK, otherwise, don't bother trying to crack it. There is another important difference between cracking WPA/WPA2 and WEP. This is the approach used to crack the WPA/WPA2 pre-shared key. Unlike WEP, where statistical methods can be used to speed up the cracking process, only plain brute force techniques can be used against WPA/WPA2. That is, because the key is not static, so collecting IVs like when cracking WEP encryption, does not speed up the attack. The only thing that does give the information to start an attack is the handshake between client and AP. Handshaking is done when the client connects to the network. Although not absolutely true, for the purposes of this tutorial, consider it true. Since the pre-shared key can be from 8 to 63 characters in length, it effectively becomes impossible to crack the pre-shared key. The only time you can crack the pre-shared key is if it is a dictionary word or relatively short in length. Conversely, if you want to have an unbreakable wireless network at home, use WPA/WPA2 and a 63 character password composed of random characters including special symbols. The impact of having to use a brute force approach is substantial. Because it is very compute intensive, a computer can only test 50 to 300 possible keys per second depending on the computer CPU. It can take hours, if not days, to crunch through a large dictionary. If you are thinking about generating your own password list to cover all the permutations and combinations of characters and special symbols, check out this brute force time calculator [ first. You will be very surprised at how much time is required. IMPORTANT This means that the passphrase must be contained in the dictionary you are using to break WPA/WPA2. If it is not in the dictionary then aircrack-ng will be unable to determine the key. There is no difference between cracking WPA or WPA2 networks. The authentication methodology is basically the same between them. So the techniques you use are identical. It is recommended that you experiment with your home wireless access point to get familiar with these ideas and techniques. If you do not own a particular access point, please remember to get permission from the owner prior to playing with it. I would like to acknowledge and thank the Aircrack-ng team [ for producing such a great robust tool. Please send me any constructive feedback, positive or negative. Additional troubleshooting ideas and tips are especially welcome. 1 of 10 07/08/ :02 PM
2 Assumptions First, this solution assumes: You are using drivers patched for injection. Use the injection test to confirm your card can inject. You are physically close enough to send and receive access point and wireless client packets. Remember that just because you can receive packets from them does not mean you may will be able to transmit packets to them. The wireless card strength is typically less then the AP strength. So you have to be physically close enough for your transmitted packets to reach and be received by both the AP and the wireless client. You can confirm that you can communicate with the specific AP by following these instructions. You are using v0.9.1 or above of aircrack-ng. If you use a different version then some of the command options may have to be changed. Ensure all of the above assumptions are true, otherwise the advice that follows will not work. In the examples below, you will need to change ath0 to the interface name which is specific to your wireless card. Equipment used In this tutorial, here is what was used: MAC address of PC running aircrack-ng suite: 00:0F:B5:88:AC:82 MAC address of the wireless client using WPA2: 00:0F:B5:FD:FB:C2 BSSID (MAC address of access point): 00:14:6C:7E:40:80 ESSID (Wireless network name): teddy Access point channel: 9 Wireless interface: ath0 You should gather the equivalent information for the network you will be working on. Then just change the values in the examples below to the specific network. Solution Solution Overview The objective is to capture the WPA/WPA2 authentication handshake and then use aircrack-ng to crack the pre-shared key. This can be done either actively or passively. Actively means you will accelerate the process by deauthenticating an existing wireless client. Passively means you simply wait for a wireless client to authenticate to the WPA/WPA2 network. The advantage of passive is that you don't actually need injection capability and thus the Windows version of aircrack-ng can be used. Here are the basic steps we will be going through: Start the wireless interface in monitor mode on the specific AP channel Start airodump-ng on AP channel with filter for bssid to collect authentication handshake Use aireplay-ng to deauthenticate the wireless client Run aircrack-ng to crack the pre-shared key using the authentication handshake 2 of 10 07/08/ :02 PM
3 Step 1 - Start the wireless interface in monitor mode The purpose of this step is to put your card into what is called monitor mode. Monitor mode is the mode whereby your card can listen to every packet in the air. Normally your card will only hear packets addressed to you. By hearing every packet, we can later capture the WPA/WPA2 4-way handshake. As well, it will allow us to optionally deauthenticate a wireless client in a later step. The exact procedure for enabling monitor mode varies depending on the driver you are using. To determine the driver (and the correct procedure to follow), run the following command: airmon-ng On a machine with a Ralink, an Atheros and a Broadcom wireless card installed, the system responds: Interface Chipset Driver rausb0 Ralink RT73 rt73 wlan0 Broadcom b43 - [phy0] wifi0 Atheros madwifi-ng ath0 Atheros madwifi-ng VAP (parent: wifi0) The presence of a [phy0] tag at the end of the driver name is an indicator for mac80211, so the Broadcom card is using a mac80211 driver. Note that mac80211 is supported only since aircrack-ng v1.0-rc1, and it won't work with v Both entries of the Atheros card show madwifi-ng as the driver - follow the madwifi-ng-specific steps to set up the Atheros card. Finally, the Ralink shows neither of these indicators, so it is using an ieee80211 driver - see the generic instructions for setting it up. Step 1a - Setting up madwifi-ng First stop ath0 by entering: airmon-ng stop ath0 The system responds: Interface Chipset Driver wifi0 Atheros madwifi-ng ath0 Atheros madwifi-ng VAP (parent: wifi0) (VAP destroyed) Enter iwconfig to ensure there are no other athx interfaces. It should look similar to this: lo eth0 wifi0 If there are any remaining athx interfaces, then stop each one. When you are finished, run iwconfig to ensure there are none left. Now, enter the following command to start the wireless card on channel 9 in monitor mode: airmon-ng start wifi0 9 Note: In this command we use wifi0 instead of our wireless interface of ath0. This is because the 3 of 10 07/08/ :02 PM
4 madwifi-ng drivers are being used. The system will respond: Interface Chipset Driver wifi0 Atheros madwifi-ng ath0 Atheros madwifi-ng VAP (parent: wifi0) (monitor mode enabled) You will notice that ath0 is reported above as being put into monitor mode. To confirm the interface is properly setup, enter iwconfig. The system will respond: lo wifi0 eth0 ath0 IEEE g ESSID:' Nickname:' Mode:Monitor Frequency:2.452 GHz Access Point: 00:0F:B5:88:AC:82 Bit Rate:0 kb/s Tx-Power:18 dbm Sensitivity=0/3 Retry:off RTS thr:off Fragment thr:off Encryption key:off Power Management:off Link Quality=0/94 Signal level=-95 dbm Noise level=-95 dbm Rx invalid nwid:0 Rx invalid crypt:0 Rx invalid frag:0 Tx excessive retries:0 Invalid misc:0 Missed beacon:0 In the response above, you can see that ath0 is in monitor mode, on the 2.452GHz frequency which is channel 9 and the Access Point shows the MAC address of your wireless card. Only the madwifi-ng drivers show the card MAC address in the AP field, other drivers do not. So everything is good. It is important to confirm all this information prior to proceeding, otherwise the following steps will not work properly. To match the frequency to the channel, check out: /channel/deployment/guide/channel.html#wp [ /channel/deployment/guide/channel.html#wp134132]. This will give you the frequency for each channel. Step 1b - Setting up mac80211 drivers Unlike madwifi-ng, you do not need to remove the wlan0 interface when setting up mac80211 drivers. Instead, use the following command to set up your card in monitor mode on channel 9: airmon-ng start wlan0 9 The system responds: Interface Chipset Driver wlan0 Broadcom b43 - [phy0] (monitor mode enabled on mon0) Notice that airmon-ng enabled monitor-mode on mon0. So, the correct interface name to use in later parts of the tutorial is mon0. Wlan0 is still in regular (managed) mode, and can be used as usual, provided that the AP that wlan0 is connected to is on the same channel as the AP you are attacking, and you are not performing any channel-hopping. To confirm successful setup, run iwconfig. The following output should appear: 4 of 10 07/08/ :02 PM
5 lo eth0 wmaster0 wlan0 mon0 IEEE bg ESSID:' Mode:Managed Frequency:2.452 GHz Access Point: Not-Associated Tx-Power=0 dbm Retry min limit:7 RTS thr:off Fragment thr=2352 B Encryption key:off Power Management:off Link Quality:0 Signal level:0 Noise level:0 Rx invalid nwid:0 Rx invalid crypt:0 Rx invalid frag:0 Tx excessive retries:0 Invalid misc:0 Missed beacon:0 IEEE bg Mode:Monitor Frequency:2.452 GHz Tx-Power=0 dbm Retry min limit:7 RTS thr:off Fragment thr=2352 B Encryption key:off Power Management:off Link Quality:0 Signal level:0 Noise level:0 Rx invalid nwid:0 Rx invalid crypt:0 Rx invalid frag:0 Tx excessive retries:0 Invalid misc:0 Missed beacon:0 Here, mon0 is seen as being in monitor mode, on channel 9 (2.452GHz). Unlike madwifi-ng, the monitor interface has no Access Point field at all. Also notice that wlan0 is still present, and in managed mode - this is normal. Because both interfaces share a common radio, they must always be tuned to the same channel - changing the channel on one interface also changes channel on the other one. Step 1c - Setting up other drivers For other (ieee80211-based) drivers, simply run the following command to enable monitor mode (replace rausb0 with your interface name): airmon-ng start rausb0 9 The system responds: Interface Chipset Driver rausb0 Ralink rt73 (monitor mode enabled) At this point, the interface should be ready to use. Step 2 - Start airodump-ng to collect authentication handshake The purpose of this step is to run airodump-ng to capture the 4-way authentication handshake for the AP we are interested in. Enter: airodump-ng -c 9 --bssid 00:14:6C:7E:40:80 -w psk ath0 Where: -c 9 is the channel for the wireless network --bssid 00:14:6C:7E:40:80 is the access point MAC address. This eliminates extraneous traffic. -w psk is the file name prefix for the file which will contain the IVs. 5 of 10 07/08/ :02 PM
6 ath0 is the interface name. Important: Do NOT use the --ivs option. You must capture the full packets. Here what it looks like if a wireless client is connected to the network: CH 9 ][ Elapsed: 4 s ][ :58 ][ WPA handshake: 00:14:6C:7E:40:80 BSSID PWR RXQ Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID 00:14:6C:7E:40: WPA2 CCMP PSK teddy BSSID STATION PWR Lost Packets Probes 00:14:6C:7E:40:80 00:0F:B5:FD:FB:C In the screen above, notice the WPA handshake: 00:14:6C:7E:40:80 in the top right-hand corner. This means airodump-ng has successfully captured the four-way handshake. Here it is with no connected wireless clients: CH 9 ][ Elapsed: 4 s ][ :51 BSSID PWR RXQ Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID 00:14:6C:7E:40: WPA2 CCMP PSK teddy BSSID STATION PWR Lost Packets Probes Troubleshooting Tip See the Troubleshooting Tips section below for ideas. To see if you captured any handshake packets, there are two ways. Watch the airodump-ng screen for WPA handshake: 00:14:6C:7E:40:80 in the top right-hand corner. This means a four-way handshake was successfully captured. See just above for an example screenshot. Use Wireshark and apply a filter of eapol. This displays only eapol packets you are interested in. Thus you can see if capture contains 0,1,2,3 or 4 eapol packets. Step 3 - Use aireplay-ng to deauthenticate the wireless client This step is optional. If you are patient, you can wait until airodump-ng captures a handshake when one or more clients connect to the AP. You only perform this step if you opted to actively speed up the process. The other constraint is that there must be a wireless client currently associated with the AP. If there is no wireless client currently associated with the AP, then you have to be patient and wait for one to connect to the AP so that a handshake can be captured. Needless to say, if a wireless client shows up later and airodump-ng did not capture the handshake, you can backtrack and perform this step. This step sends a message to the wireless client saying that that it is no longer associated with the AP. The wireless client will then hopefully reauthenticate with the AP. The reauthentication is what generates the 4-way authentication handshake we are interested in collecting. This is what we use to break the WPA/WPA2 pre-shared key. Based on the output of airodump-ng in the previous step, you determine a client which is currently connected. You need the MAC address for the following. Open another console session and enter: aireplay-ng a 00:14:6C:7E:40:80 -c 00:0F:B5:FD:FB:C2 ath0 6 of 10 07/08/ :02 PM
7 Where: -0 means deauthentication 1 is the number of deauths to send (you can send multiple if you wish) -a 00:14:6C:7E:40:80 is the MAC address of the access point -c 00:0F:B5:FD:FB:C2 is the MAC address of the client you are deauthing ath0 is the interface name Here is what the output looks like: 11:09:28 Sending DeAuth to station -- STMAC: [00:0F:B5:34:30:30] With luck this causes the client to reauthenticate and yield the 4-way handshake. Troubleshooting Tips The deauthentication packets are sent directly from your PC to the clients. So you must be physically close enough to the clients for your wireless card transmissions to reach them. To confirm the client received the deauthentication packets, use tcpdump or similar to look for ACK packets back from the client. If you did not get an ACK packet back, then the client did not hear the deauthentication packet. Step 4 - Run aircrack-ng to crack the pre-shared key The purpose of this step is to actually crack the WPA/WPA2 pre-shared key. To do this, you need a dictionary of words as input. Basically, aircrack-ng takes each word and tests to see if this is in fact the pre-shared key. There is a small dictionary that comes with aircrack-ng - password.lst. This file can be found in the test directory of the aircrack-ng source code. The Wiki FAQ has an extensive list of dictionary sources. You can use John the Ripper [ (JTR) to generate your own list and pipe them into aircrack-ng. Using JTR in conjunction with aircrack-ng is beyond the scope of this tutorial. Open another console session and enter: aircrack-ng -w password.lst -b 00:14:6C:7E:40:80 psk*.cap Where: -w password.lst is the name of the dictionary file. Remember to specify the full path if the file is not located in the same directory. *.cap is name of group of files containing the captured packets. Notice in this case that we used the wildcard * to include multiple files. Here is typical output when there are no handshakes found: Opening psk-01.cap Opening psk-02.cap Opening psk-03.cap Opening psk-04.cap Read 1827 packets. No valid WPA handshakes found. 7 of 10 07/08/ :02 PM
8 When this happens you either have to redo step 3 (deauthenticating the wireless client) or wait longer if you are using the passive approach. When using the passive approach, you have to wait until a wireless client authenticates to the AP. Here is typical output when handshakes are found: Opening psk-01.cap Opening psk-02.cap Opening psk-03.cap Opening psk-04.cap Read 1827 packets. # BSSID ESSID Encryption 1 00:14:6C:7E:40:80 teddy WPA (1 handshake) Choosing first network as target. Now at this point, aircrack-ng will start attempting to crack the pre-shared key. Depending on the speed of your CPU and the size of the dictionary, this could take a long time, even days. Here is what successfully cracking the pre-shared key looks like: Aircrack-ng 0.8 [00:00:00] 2 keys tested (37.20 k/s) KEY FOUND! [ ] Master Key : CD 69 0D 11 8E AC AA C5 C5 EC BB D 49 3E B8 A6 13 C5 4A ED C3 7E 2C 59 5E AB FD Transcient Key : 06 F8 BB F3 B1 55 AE EE 1F 66 AE 51 1F F CE 8A 9D A0 FC ED A6 DE BA E CD 40 FF 1D 41 E E BF D5 4A 5E 2B C EA A E0 71 EAPOL HMAC : 4E 27 D9 5B C 66 C8 B1 29 D1 CB Troubleshooting Tips I Cannot Capture the Four-way Handshake! It can sometimes be tricky to capture the four-way handshake. Here are some troubleshooting tips to address this: Your monitor card must be in the same mode as the both the client and Access Point. So, for example, if your card was in B mode and the client/ap were using G mode, then you would not capture the handshake. This is especially important for new APs and clients which may be turbo mode and/or other new standards. Some drivers allow you to specify the mode. Also, iwconfig has an option modulation that can sometimes be used. Do man iwconfig to see the options for modulation. For information, 1, 2, 5.5 and 11Mbit are 'b', 6, 9, 12, 18, 24, 36, 48, 54Mbit are 'g'. Sometimes you also need to set the monitor-mode card to the same speed. IE auto, 1MB, 2MB, 11MB, 54MB, etc. Be sure that your capture card is locked to the same channel as the AP. You can do this by 8 of 10 07/08/ :02 PM
9 specifying -c <channel of AP> when you start airodump-ng. Be sure there are no connection managers running on your system. This can change channels and/or change mode without your knowledge. You are physically close enough to receive both access point and wireless client packets. The wireless card strength is typically less then the AP strength. Conversely, if you are too close then the received packets can be corrupted and discarded. So you cannot be too close. Make sure to use the drivers specified on the wiki. Depending on the driver, some old versions do not capture all packets. Ideally, connect and disconnect a wireless client normally to generate the handshake. If you use the deauth technique, send the absolute minimum of packets to cause the client to reauthenticate. Normally this is a single deauth packet. Sending an excessive number of deauth packets may cause the client to fail to reconnect and thus it will not generate the four-way handshake. As well, use directed deauths, not broadcast. To confirm the client received the deauthentication packets, use tcpdump or similar to look for ACK packets back from the client. If you did not get an ACK packet back, then the client did not hear the deauthentication packet. Try stopping the radio on the client station then restarting it. Make sure you are not running any other program/process that could interfere such as connection managers, Kismet, etc. Review your captured data using the WPA Packet Capture Explained tutorial to see if you can identify the problem. Such as missing AP packets, missing client packets, etc. Unfortunately, sometimes you need to experiment a bit to get your card to properly capture the four-way handshake. The point is, if you don't get it the first time, have patience and experiment a bit. It can be done! Another approach is to use Wireshark to review and analyze your packet capture. This can sometimes give you clues as to what is wrong and thus some ideas on how to correct it. The WPA Packet Capture Explained tutorial is a companion to this tutorial and walks you through what a normal WPA connection looks like. As well, see the FAQ for detailed information on how to use Wireshark. In an ideal world, you should use a wireless device dedicated to capturing the packets. This is because some drivers such as the RTL8187L driver do not capture packets the card itself sends. Also, always use the driver versions specified on the wiki. This is because some older versions of the drivers such as the RT73 driver did not capture client packets. When using Wireshark, the filter eapol will quickly display only the EAPOL packets. Based on what EAPOL packets are actually in the capture, determine your correction plan. For example, if you are missing the client packets then try to determine why and how to collect client packets. To dig deep into the packet analysis, you must start airodump-ng without a BSSID filter and specify the capture of the full packet, not just IVs. Needless to say, it must be locked to the AP channel. The reason for eliminating the BSSID filter is to ensure all packets including acknowledgments are captured. With a BSSID filter, certain packets are dropped from the capture. Every packet sent by client or AP must be acknowledged. This is done with an acknowledgment packet which has a destination MAC of the device which sent the original packet. If you are trying to deauthenticate a client, one thing to check is that you receive the ack packet. This confirms the client received the deauth packet. Failure to receive the ack packet likely means that the client is out of transmission range. Thus failure. When it comes to analyzing packet captures, it is impossible to provide detailed instructions. I have touched on some techniques and areas to look at. This is an area which requires effort to build your skills 9 of 10 07/08/ :02 PM
10 on both WPA/WPA2 plus how to use Wireshark. aircrack-ng says '0 handshakes' Check the I Cannot Capture the Four-way Handshake! troubleshooting tip. aircrack-ng says 'No valid WPA handshakes found' Check the I Cannot Capture the Four-way Handshake! troubleshooting tip. cracking_wpa.txt Last modified: 2010/08/29 19:44 by mister_x Except where otherwise noted, content on this wiki is licensed under the following license:cc Attribution- Noncommercial-Share Alike 3.0 Unported [ 10 of 10 07/08/ :02 PM
Wireless LAN Pen-Testing. Part I
Wireless LAN Pen-Testing Part I To know your Enemy, you must become your Enemy (Sun Tzu, 600 BC) Georg Penn 23.03.2012 Motivation Read manuals, documentation, standards Check sources for their reliability,
More information0) What is the wpa handhake?
We have already seen how easy it is with time and the right tools to get the WEP key of any wireless network. We have already explained that these operations are not lawful but for pure interest and personal
More informationWiFi Security Assessments
WiFi Security Assessments Robert Dooling Dooling Information Security Defenders (DISD) December, 2009 This work is licensed under a Creative Commons Attribution 3.0 Unported License. Table of Contents
More informationWireless Sniffing with Wireshark
ethereal_ch06.qxd 11/8/06 5:07 PM Page 1 Chapter 6 Wireless Sniffing with Wireshark Solutions in this chapter: Techniques for Effective Wireless Sniffing Understanding Wireless Card Operating Modes Configuring
More informationWEP WPA WPS :: INDEX : Introduction :
WEP WPA WPS With clients Without clients :: INDEX : Introduction > Overview > Terms & Definitions [ Step 1 ] : Configuring the network interface [ Step 2 ] : Collecting the network info [ Step 3 ] : Capturing
More informationMITM Man in the Middle
MITM Man in the Middle Wifi Packet Capturing and Session Hijacking using Wireshark Introduction The main Objective of this Attack is to make a Fake Access point and send the fake ARP Packets on same Wi-Fi
More informationKali Linux Wireless Penetration Testing Essentials
Fr Kali Linux is the most popular distribution dedicated to penetration testing that includes a set of free, open source tools. This book introduces you to wireless penetration testing and describes how
More informationWireless Network Security. Pat Wilbur Wireless Networks March 30, 2007
Wireless Network Security Pat Wilbur Wireless Networks March 30, 2007 Types of Attacks Intrusion gain unauthorized access to a network in order to use the network or Internet connection Types of Attacks
More informationWireless Pre-Shared Key Cracking (WPA, WPA2)
Wireless Pre-Shared Key Cracking (WPA, WPA2) TABLE OF CONTENTS Introduction.. 2 Mechanics Of PSKs And How They Work Demystified.. 2 How PSKs Can Be Cracked!.. 5 WPA2 PSK Cracking Demonstration.. 6
More informationS-38.2131/3133 Networking Technology, laboratory course A/B
A! Aalto University School of Electrical Engineering Department of Communications and Networking S-38.2131/3133 Networking Technology, laboratory course A/B Student edition Anni Matinlauri, 3.1.2007 Tuomas
More informationN600 WiFi USB Adapter
Model WNDA3100v3 User Manual December 2014 202-11470-01 350 East Plumeria Drive San Jose, CA 95134 USA Support Thank you for selecting NETGEAR products. After installing your device, locate the serial
More informationLab Exercise 802.11. Objective. Requirements. Step 1: Fetch a Trace
Lab Exercise 802.11 Objective To explore the physical layer, link layer, and management functions of 802.11. It is widely used to wireless connect mobile devices to the Internet, and covered in 4.4 of
More informationLevelOne User Manual WPC-0600 N_One Wireless CardBus Adapter
LevelOne User Manual WPC-0600 N_One Wireless CardBus Adapter V2.0.0-0712 Safety FCC WARNING This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to
More informationTube-U(G) Long-Range Outdoor IEEE 802.11g USB Adapter User s Guide
Tube-U(G) Long-Range Outdoor IEEE 802.11g USB Adapter User s Guide Alfa Network, Inc. Page 1 Table of Content Over view.. 3 Unpacking information.. 3 Introduction to the Tube-U(G) outdoor USB Adapter..
More informationLong-Range 500mW IEEE 802.11g Wireless USB Adapter. User's Guide
Long-Range 500mW IEEE 802.11g Wireless USB Adapter User's Guide TABLE OF CONTENTS OVERVIEW.. 4 UNPACKING INFORMATION.. 4 INTRODUCTION TO THE IEEE 802.11G WIRELESS USB ADAPTER.. 5 Key Features..5 INSTALLATION
More informationVulnerabilities of Wireless Security protocols (WEP and WPA2)
Vulnerabilities of Wireless Security protocols (WEP and WPA2) Vishal Kumkar, Akhil Tiwari, Pawan Tiwari, Ashish Gupta, Seema Shrawne Abstract - Wirelesses Local Area Networks (WLANs) have become more prevalent
More informationUNIK4250 Security in Distributed Systems University of Oslo Spring 2012. Part 7 Wireless Network Security
UNIK4250 Security in Distributed Systems University of Oslo Spring 2012 Part 7 Wireless Network Security IEEE 802.11 IEEE 802 committee for LAN standards IEEE 802.11 formed in 1990 s charter to develop
More informationTable of Contents. Cisco Wi Fi Protected Access 2 (WPA 2) Configuration Example
Table of Contents Wi Fi Protected Access 2 (WPA 2) Configuration Example..1 Document ID: 67134..1 Introduction..1 Prerequisites..1 Requirements..1 Components Used..2 Conventions..2 Background Information..2
More information
Linksys WAP300N. User Guide
User Guide Contents Contents Overview Package contents 1 Back view 1 Bottom view 2 How to expand your home network 3 What is a network? 3 How to expand your home network 3 Where to find more help 3 Operating
More informationLink Link sys E3000 sys RE1000
User Guide High Performance Extender Wireless-N Router Linksys Linksys RE1000 E3000Wireless-N Table of Contents Contents Chapter 1: Product Overview 1 Front 1 Top 1 Bottom 1 Back 2 Chapter 2: Advanced
More informationSecurity+ Guide to Network Security Fundamentals, Third Edition. Chapter 6. Wireless Network Security
Security+ Guide to Network Security Fundamentals, Third Edition Chapter 6 Wireless Network Security Objectives Overview of IEEE 802.11 wireless security Define vulnerabilities of Open System Authentication,
More informationMethodology: Security plan for wireless networks. By: Stephen Blair Mandeville A. Summary
Methodology: Security plan for wireless networks By: Stephen Blair Mandeville A. Summary The evolution to wireless networks allows connections with the same quality of data transfer at a lower cost but
More informationAn Experimental Study Analysis of Security Attacks at IEEE 802.11 Wireless Local Area Network
, pp. 9-18 http://dx.doi.org/10.14257/ijfgcn.2015.8.1.02 An Experimental Study Analysis of Security Attacks at IEEE 802.11 Wireless Local Area Network 1 Md Waliullah, 2 A B M Moniruzzaman and 3 Md. Sadekur
More informationKali Linux Cookbook. Willie L. Pritchett David De Smet. Chapter No. 9 'Wireless Attacks'
Kali Linux Cookbook Willie L. Pritchett David De Smet Chapter No. 9 'Wireless Attacks' In this package, you will find: A Biography of the authors of the book A preview chapter from the book, Chapter NO.9
More information802.11 Security (WEP, WPAWPA2) 19/05/2009. Giulio Rossetti Unipi Giulio.Rossetti@gmail.com
802.11 Security (WEP, WPAWPA2) 19/05/2009 Giulio Rossetti Unipi Giulio.Rossetti@gmail.com 802.11 Security Standard: WEP Wired Equivalent Privacy The packets are encrypted, before sent, with a Secret Key
More informationWifi Web Server Module w TF Socket User s Guide
Wifi Web Server Module w TF Socket User s Guide 2004-2010 Sure Electronics Inc. MB-CM14117_Ver1.0 WIFI WEB SERVER MODULE W TF SOCKET USER S GUIDE Table of Contents Chapter 1. Overview..1 1.1 Overview..
More informationThese notes are derived from the wireless course run at B Sides Delaware 2013.
Shingeki no kyojin episode 23 sub indo samehadaku dragon. Wireless Course: Wi Fi Tools These notes are derived from the wireless course run at B Sides Delaware 2013. Michael Kershaw, Russell Handorf, 2013 The content is provided under the CC BY SA license. An
More informationGolden N Wireless Mini USB Adapter. Model # AWLL6075 User s Manual. Rev. 1.2
Golden N Wireless Mini USB Adapter Model # AWLL6075 User s Manual Rev. 1.2 Table of Contents 1. Introduction..2 1.1 Package Contents..2 1.2 Features..2 2. Install the Wireless Adapter..3 3. Connect
More informationGuide for wireless environments
Sanako Study Guide for wireless environments 1 Contents Sanako Study.. 1 Guide for wireless environments.. 1 What will you find in this guide?.. 3 General.. 3 Disclaimer.. 3 Requirements in brief..
More informationWireless N 300 Mini USB Adapter. Model # AWLL6086 User s Manual. Rev. 1.0
Wireless N 300 Mini USB Adapter Model # AWLL6086 User s Manual Rev. 1.0 Table of Contents 1. Introduction..2 1.1 Package Contents..2 1.2 Features..2 2. Install the Wireless Adapter..3 3. Install the
More informationWorkshop Presentation Chapter4. Yosuke TANAKA
Workshop Presentation Chapter4 Yosuke TANAKA Agenda(Framing in Detail) Data Frames Control Frames type RTS Duration CTS Addressing (!!important!!) Variation on Data Frame Theme Applied Data Framing ACK
More informationVIDEO Intypedia012en LESSON 12: WI FI NETWORKS SECURITY. AUTHOR: Raúl Siles. Founder and Security Analyst at Taddong
VIDEO Intypedia012en LESSON 12: WI FI NETWORKS SECURITY AUTHOR: Raúl Siles Founder and Security Analyst at Taddong Hello and welcome to Intypedia. Today we will talk about the exciting world of security
More informationUser Guide. E-Series Routers
User Guide E-Series Routers Table of Contents Table of Contents Product overview E900/E1200/E1500/E2500/E3200 1 Back view 1 Bottom view 1 E4200 2 Top view 2 Back view 2 Setting Up Your E-Series Router
More information9 Simple steps to secure your Wi-Fi Network.
9 Simple steps to secure your Wi-Fi Network. Step 1: Change the Default Password of Modem / Router After opening modem page click on management - access control password. Select username, confirm old password
More informationOSBRiDGE 5XLi. Configuration Manual. Firmware 3.10R
OSBRiDGE 5XLi Configuration Manual Firmware 3.10R 1. Initial setup and configuration. OSBRiDGE 5XLi devices are configurable via WWW interface. Each device uses following default settings: IP Address:
More informationWIRELESS SECURITY. Information Security in Systems & Networks Public Development Program. Sanjay Goel University at Albany, SUNY Fall 2006
WIRELESS SECURITY Information Security in Systems & Networks Public Development Program Sanjay Goel University at Albany, SUNY Fall 2006 1 Wireless LAN Security Learning Objectives Students should be able
More informationBasic Wireless Configuration and Security
Basic Wireless Configuration and Security This quick start guide provides basic wireless configuration information for the ProSafe Wireless-N 8-Port Gigabit VPN Firewall FVS318N. For information about
More informationSecurity in IEEE 802.11 WLANs
Security in IEEE 802.11 WLANs 1 IEEE 802.11 Architecture Extended Service Set (ESS) Distribution System LAN Segment AP 3 AP 1 AP 2 MS MS Basic Service Set (BSS) Courtesy: Prashant Krishnamurthy, Univ Pittsburgh
More informationWIB250A5 Series PC/104+ 802.11b/g/a/h WLAN Modules
Product Overview WIB250A5 series are full-featured wireless devices that use the PC/104 Plus form factor. WIB250A5 works with PC/104 Plus and PCI-104 CPU modules and upgrades your embedded system into
More informationWRE2205. User s Guide. Quick Start Guide. Wireless N300 Range Extender. Default Login Details. Version 1.00 Edition 1, 06/2012
WRE2205 Wireless N300 Range Extender Version 1.00 Edition 1, 06/2012 Quick Start Guide User s Guide Default Login Details LAN IP Address http://192.168.1.2 User Name admin Passwordwww.zyxel.com 1234 Copyright
More informationDV230 Web Based Configuration Troubleshooting Guide
DV230 Web Based Configuration Troubleshooting Guide 1. Login settings After getting a DHCP IP address from your P1 W1MAX Modem DV-230), open any Internet browser and type in the URL address: http://10.1.1.254
More informationAirPcap User s Guide. May 2013
AirPcap User s Guide May 2013 2013 Riverbed Technology. All rights reserved. Accelerate, AirPcap, BlockStream, Cascade, Cloud Steelhead, Granite, Interceptor, RiOS, Riverbed, Shark, SkipWare, Steelhead,
More informationWpa2 Crack Windows
WEP Overview 1/2. and encryption mechanisms Now deprecated. Shared key Open key (the client will authenticate always) Shared key authentication
WLAN Security WEP Overview 1/2 WEP, Wired Equivalent Privacy Introduced in 1999 to provide confidentiality, authentication and integrity Includes weak authentication Shared key Open key (the client will
More informationA Division of Cisco Systems, Inc. GHz 2.4 802.11g. Wireless-G. USB Network Adapter with RangeBooster. User Guide WIRELESS WUSB54GR. Model No.
A Division of Cisco Systems, Inc. GHz 2.4 802.11g WIRELESS Wireless-G USB Network Adapter with RangeBooster User Guide Model No. WUSB54GR Copyright and Trademarks Specifications are subject to change without
More informationWIRELESS SECURITY TOOLS
WIRELESS SECURITY TOOLS Johanna Janse van Rensburg, Barry Irwin Rhodes University G01j202j7@campus.ru.ac.za, b.irwin@ru.ac.za (083) 944 3924 Computer Science Department, Hamilton Building, Rhodes University
More informationThe Wireless Network Road Trip
The Wireless Network Road Trip The Association Process To begin, you need a network. This lecture uses the common logical topology seen in Figure 9-1. As you can see, multiple wireless clients are in
More informationIntroduction to WiFi Security. Frank Sweetser WPI Network Operations and Security fs@wpi.edu
Introduction to WiFi Security Frank Sweetser WPI Network Operations and Security fs@wpi.edu Why should I care? Or, more formally what are the risks? Unauthorized connections Stealing bandwidth Attacks
More informationKvaser BlackBird Getting Started Guide
Kvaser BlackBird Getting Started Guide Copyright 2007-2011 Kvaser AB, Mölndal, Sweden http://www.kvaser.com Last updated Wednesday, 18 September 2013 We believe that the information contained herein was
More informationWAP3205 v2. User s Guide. Quick Start Guide. Wireless N300 Access Point. Default Login Details. Version 1.00 Edition 2, 10/2015
WAP3205 v2 Wireless N300 Access Point Version 1.00 Edition 2, 10/2015 Quick Start Guide User s Guide Default Login Details Web Address http://zyxelsetup Password www.zyxel.com 1234 Copyright 2014 ZyXEL
More informationDesigning, Securing and Monitoring 802.11a/b/g/n Wireless Networks
Designing, Securing and Monitoring 802.11a/b/g/n Wireless Networks The importance of Wireless today Increasingly in the Corporate Environment, Wireless is becoming an enabling technology to facilitate
More informationIEEE 802.11bg Mode:Monitor Frequency:2.437 GHz Tx-Power=20 dbm
root@bt:~# airmon-ng Interface Chipset Driver wlan0 wlan1 Ralink 2570 USB rt2500usb - [phy1] Intel 3945ABG iwl3945 - [phy0] root@bt:~# airmon-ng start wlan0 Interface Chipset Driver wlan0 Ralink 2570 USB
More informationA Division of Cisco Systems, Inc. GHz 2.4 802.11g. Wireless-G. Access Point with SRX. User Guide WIRELESS WAP54GX. Model No.
A Division of Cisco Systems, Inc. GHz 2.4 802.11g WIRELESS Wireless-G Access Point with SRX User Guide Model No. WAP54GX Copyright and Trademarks Specifications are subject to change without notice. Linksys
More informationMN-700 Base Station Configuration Guide
MN-700 Base Station Configuration Guide Contents pen the Base Station Management Tool..3 Log ff the Base Station Management Tool..3 Navigate the Base Station Management Tool..4 Current Base Station
More informationCapture and analysis of 802.11 wireless traffic
Capture and analysis of 802.11 wireless traffic October 2012 Ver. 1.00 Copyright Connect One Ltd., 2008-2012 The information in this document is subject to change without notice and shall not be construed
More informationEPI-3601S Wireless LAN PCI adapter Version 1.2 EPI-3601S. Wireless LAN PCI Adapter. (802.11g & 802.11b up to 108 Mbps) User Manual. Version: 1.
EPI-3601S Wireless LAN PCI Adapter (802.11g & 802.11b up to 108 Mbps) User Manual Version: 1.2 1 TABLE OF CONTENTS 1 INTRODUCTION..3 2 FEATURES..3 3 PACKAGE CONTENTS..4 4 SYSTEM REQUIREMENTS..5 5 INSTALLATION..5
More informationAP60. Wireless-N POE Access Point. User s Manual
AP60 Wireless-N POE Access Point User s Manual Copyright and Disclaimer Copyright & Disclaimer No part of this publication may be reproduced in any form or by any means, whether electronic, mechanical,
More informationProgramming Wireless Security. GAWN Gold Certification. Author: Robin Wood, robin@freedomsoftware.co.uk. Adviser:Joey Neim
Programming Wireless Security GAWN Gold Certification Author: Robin Wood, robin@freedomsoftware.co.uk Adviser:Joey Neim Accepted: November 12th 2007 Robin Wood 1 Table of Contents 1 Introduction..5 2
Backtrack 5r3 Download Windows 10
More informationG.DUO. Dual 11g Access Point. User s Manual
G.DUO Dual 11g Access Point User s Manual Copyright and Disclaimer Copyright & Disclaimer No part of this publication may be reproduced in any form or by any means, whether electronic, mechanical, photocopying,
More informationUSER GUIDE AC2400. DUAL BAND GIGABIT Wi Fi ROUTER. Model# E8350
USER GUIDE AC2400 DUAL BAND GIGABIT Wi Fi ROUTER Model# E8350 Table of Contents Product overview E8350................... 1 Setting Up Your E-Series Router Where to find more help.............
More information300Mbps Wireless N Ceiling Mount Access Point
Datasheet Ceiling Mount Access Point 110 Highlights Wireless N speed up to 300Mbps Controller Software enables administrators to easily manage hundreds of s Supports passive PoE for convenient installation
More informationWireless N 150 USB Adapter with 10dBi High Gain Antenna. Model # AWLL5055 User s Manual. Rev. 1.0
Wireless N 150 USB Adapter with 10dBi High Gain Antenna Model # AWLL5055 User s Manual Rev. 1.0 Table of Contents 1. Introduction..2 1.1 Package Contents..2 1.2 Features..2 2. Install Wireless USB Adapter..3
More informationTutorial on Network Management and Measurements. Tasos Alexandridis analexan@csd.uoc.gr
Tutorial on Network Management and Measurements Tasos Alexandridis analexan@csd.uoc.gr Network management Simple Network Management Protocol (SNMP) AP s SYSLOG messages Network Measurements and Analysis
More informationCS 356 Lecture 29 Wireless Security. Spring 2013
CS 356 Lecture 29 Wireless Security Spring 2013 Review Chapter 1: Basic Concepts and Terminology Chapter 2: Basic Cryptographic Tools Chapter 3 User Authentication Chapter 4 Access Control Lists Chapter
More informationChapter 2 Configuring Your Wireless Network and Security Settings
Chapter 2 Configuring Your Wireless Network and Security Settings This chapter describes how to configure the wireless features of your DG834N RangeMax TM NEXT Wireless ADSL2+ Modem Router. For a wireless
More informationLP-348. LP-Yagy2415. LP-510G/550G 54M Wireless Adapter PCMCIA/PCI. User Guide Ver:2.0 LP-5420G WWW.LANPRO.COM
LP-348 LP-Yagy2415 LP-1518 LP-5P LP-510G/550G 54M Wireless Adapter PCMCIA/PCI User Guide Ver:2.0 LP-5420G WWW.LANPRO.COM COPYRIGHT & TRADEMARKS Specifications are subject to change without notice. is a
More informationAP-90M INSTRUCTION MANUAL WIRELESS ACCESS POINT INTRODUCTION 1 BEFORE USING THE AP-90M 2 INSTALLATION GUIDE 3 CONNECTING WIRELESS LAN [BASIC]
INSTRUCTION MANUAL WIRELESS ACCESS POINT AP-90M INTRODUCTION 1 BEFORE USING THE AP-90M 2 INSTALLATION GUIDE 3 CONNECTING WIRELESS LAN [BASIC] [IEEE802.11ac] standard [IEEE802.11n] standard [IEEE802.11a/b/g]
More informationPractical Approach in Teaching Wireless LAN Security using Open Source Software
Practical Approach in Teaching Wireless LAN Security using Open Source Software Mohd Azizi Sanwani & * Kamaruddin Mamat Centre for Diploma Programme, Multimedia University Cyberjaya, MALAYSIA * Faculty
More informationBuilding secure wireless access point based on certificate authentication and firewall captive portal
EPJ Web of Conferences 68, 00029 (2014) DOI: 10.1051/ epjconf/ 20146800029 C Owned by the authors, published by EDP Sciences, 2014 Building secure wireless access point based on certificate authentication
More informationChapter 6 CDMA/802.11i
Chapter 6 CDMA/802.11i IC322 Fall 2014 Computer Networking: A Top Down Approach 6 th edition Jim Kurose, Keith Ross Addison-Wesley March 2012 Some material copyright 1996-2012 J.F Kurose and K.W. Ross,
More informationWi-Fi Settings Guide. Model No. SP 212/SP 213 Series
Wi-Fi Settings Guide Model No. SP 212/SP 213 Series Introduction There are two wireless LAN modes: infrastructure mode for connection through an access point and ad-hoc mode for establishing direct connection
More informationNWA1120 Series. User s Guide. Quick Start Guide. Wireless LAN Ceiling Mountable PoE Access Point. Default Login Details
NWA1120 Series Wireless LAN Ceiling Mountable PoE Access Point Version 1.00 Edition 1, 08/2012 Quick Start Guide User s Guide Default Login Details LAN IP Address http://192.168.1.2 User Name admin Passwordwww.zyxel.com
More informationNetComm Wireless NP920 Dual Band WiFi USB Adapter. User Guide
NetComm Wireless NP920 Dual Band WiFi USB Adapter User Guide Contents Preface.. 3 Important Safety Instructions.. 3 Introduction.. 4 Overview.. 4 Features.. 4 Package Contents.. 5 Minimum System
More informationAttacking Automatic Wireless Network Selection. Dino A. Dai Zovi and Shane A. Macaulay {ddaizovi,smacaulay1}@bloomberg.com
Attacking Automatic Wireless Network Selection Dino A. Dai Zovi and Shane A. Macaulay {ddaizovi,smacaulay1}@bloomberg.com We made Slashdot! Hackers, Meet Microsoft 'The random chatter of several hundred
More informationP r o t o l ck w fi ma a n ger User s Guide
Po rtl wifi oc manager k Portlock WiFi Manager Introduction New in version 5.08 of the Portlock Boot CD is Portlock WiFi Manager, a utility for connecting to wireless networks. It is located on the Portlock
More informationEW-7228APn User Manual
EW-7228APn User Manual 08-2012 / v1.1 1 COPYRIGHT Copyright Edimax Technology Co., Ltd. all rights reserved. No part of this publication may be reproduced, transmitted, transcribed, stored in a retrieval
 More information
More information WL-5460AP. User s Manual. 54Mbps Multi-Function Wireless AP. AirLive WL-5460AP v2 User Manual
WL-5460AP 54Mbps Multi-Function Wireless AP User s Manual 1 Copyright The contents of this publication may not be reproduced in any part or as a whole, stored, transcribed in an information retrieval system,
More informationALL0237R. Wireless N 300Mbit Access Point/Repeater. User s Manual
ALL0237R Wireless N 300Mbit Access Point/Repeater User s Manual ALLNET ALL0237R User Manual Table of Contents About the Device.. 3 Minimum System Requirements.. 5 Package Contents.. 5 Device Overview..
More informationLW310V2 Sweex Wireless 300N Router
LW310V2 Sweex Wireless 300N Router Please notice! On the included CD-ROM you will find the Setup Wizard. This easy install procedure will show you how to setup the router step-by-step. Do not expose the
More informationEW-7438RPn V2 User Manual
EW-7438RPn V2 User Manual 09-2013 / v1.0 CONTENTS I. Product Information.. 1 I-1. Package Contents.. 1 I-2. System Requirements.. 1 I-3. LED Status.. 1 I-4. Hardware Overview.. 3 I-5. Safety Information..
More informationTL-WN310G 54M Wireless CardBus Adapter
54M Wireless CardBus Adapter Rev: 1.0.1 1910010042 COPYRIGHT & TRADEMARKS Specifications are subject to change without notice. is a registered trademark of TP-LINK TECHNOLOGIES CO., LTD. Other brands and
More informationICP DAS WF-2571 FAQ. FAQ Version 1.0. ICP DAS Co., Ltd. 2014-12-23
ICP DAS WF-2571 FAQ FAQ Version 1.0 ICP DAS Co., Ltd. 2014-12-23 Table of Contents Q1: WF-2571 doesn t work at Ad-Hoc mode. What should I do?.. 3 Q2: WF-2571 doesn t work at AP mode. What should I do?..
More informationWhite paper. Testing for Wi-Fi Protected Access (WPA) in WLAN Access Points. http://www.veryxtech.com
White paper Testing for Wi-Fi Protected Access (WPA) in WLAN Access Points http://www.veryxtech.com White Paper Abstract Background The vulnerabilities spotted in the Wired Equivalent Privacy (WEP) algorithm
More informationECE 4893: Internetwork Security Lab 10: Wireless 802.11 Security
Group Number: Member Names: Date Assigned: March 23, 2004 Date Due: March 30, 2004 Last Revised: March 22, 2004 ECE 4893: Internetwork Security Lab 10: Wireless 802.11 Security Goal: The goal of this lab
More informationChapter 2 Wireless Networking Basics
Chapter 2 Wireless Networking Basics Wireless Networking Overview Some NETGEAR products conform to the Institute of Electrical and Electronics Engineers (IEEE) 802.11g standard for wireless LANs (WLANs).
More informationMitos sobre proteção de redes WiFi. Nelson Murilo http://twitter.com/nelsonmurilo
Mitos sobre proteção de redes WiFi Nelson Murilo http://twitter.com/nelsonmurilo Agenda Descrição dos mitos Onde eles falham O que funciona Nome da rede CH 10 ][ Elapsed: 9 mins ][ 2009-08-28 14:24 BSSID
More informationLevelOne WAP - 0005. User s Manual. 108 Mbps Wireless Access Point
LevelOne WAP - 0005 108 Mbps Wireless Access Point User s Manual TABLE OF CONTENTS CHAPTER 1 INTRODUCTION.. 1 Features of your Wireless Access Point.. 1 Package Contents.. 3 Physical Details.. 3 CHAPTER
More informationLOHU 4951L Outdoor Wireless Access Point / Bridge
LOHU 4951L Outdoor Wireless Access Point / Bridge Version 2.3 ------------------------------------------------------------------------------------------------------- -1- Software setup and configuration
More informationWireless security. Any station within range of the RF receives data Two security mechanism
802.11 Security Wireless security Any station within range of the RF receives data Two security mechanism A means to decide who or what can use a WLAN authentication A means to provide privacy for the
More informationUser Manual. PePWave Surf / Surf AP Indoor Series: Surf 200, E200, AP 200, AP 400. PePWave Mesh Connector Indoor Series: MC 200, E200, 400
User Manual PePWave Surf / Surf AP Indoor Series: Surf 200, E200, AP 200, AP 400 PePWave Mesh Connector Indoor Series: MC 200, E200, 400 PePWave Surf AP Series: Surf AP 200-X, E200-X, 400-X PePWave Surf
More informationWifi Penetration. Wireless Communication and Computer/Network Forensics
Wifi Penetration Wireless Communication and Computer/Network Forensics Terms Skiddy(Derogatory): Variant of 'Script Kiddy'. Hacker(Derogatory):One who builds something. Cracker(Derogatory):One who breaks
More informationWireless Access Point 300 802.11n Wireless with 4 Port 10/100 Switch
300 802.11n Wireless with 4 Port 10/100 Switch User Manual www.hamletcom.com INDEX 1. Introduction..6 1.1 System Requirements.. 6 1.2 Package Contents.. 6 2. Specification..7 2.1 LED Meaning.. 7 2.2
More informationWireless-G Access Point
USER GUIDE Model: WAP54G About This Guide About This Guide Icon Descriptions While reading through the User Guide you may see various icons that call attention to specific items. Below is a description
More informationWireless Tools. Training materials for wireless trainers
Wireless Tools Training materials for wireless trainers This talk covers tools that will show you a great deal of information about wireless networks, including network discovery, data logging, security
More informationAccess Point Configuration
Access Point Configuration Developed by IT +46 Based on the original work of: Onno Purbo and Sebastian Buettrich Goals Provide a general methodology to installation and configuration of access points Give
More information300Mbps Wireless N Gigabit Ceilling Mount Access Point
Datasheet 300Mbps Wireless N Gigabit Ceilling Mount Access Point 120 Highlights Wireless N speed up to 300Mbps Clustering function greatly simplified business wireless network management, to easy manage
More informationWireless Network Standard and Guidelines
Wireless Network Standard and Guidelines Purpose The standard and guidelines listed in this document will ensure the uniformity of wireless network access points and provide guidance for monitoring, maintaining
More informationITRAINONLINE MMTK WIRELESS CLIENT INSTALLATION HANDOUT
ITRAINONLINE MMTK WIRELESS CLIENT INSTALLATION HANDOUT Developed by: Tomas B. Krag (Linux) Bruno Roger, ESMT (Windows) Edited by: Alberto Escudero Pascual, IT +46 Table of Contents 1.
More informationAirMax5X Series. 5G High Throughput Outdoor CPE with PoE Pass through. User s Manual
AirMax5X Series 5G High Throughput Outdoor CPE with PoE Pass through User s Manual Copyright and Disclaimer Version 3.0 This guide is written for firmware version 3.0 or later. Copyright & Disclaimer No
More informationEAP9550 11N Wall Mount Access Point / WDS AP / Universal Repeater
EAP9550 is a powerful and multi-functioned 11n Access Point and it can act three modes AP/WDS/Universal Repeater. Smoke detector appearance will minimize visibility. So this model can work properly at
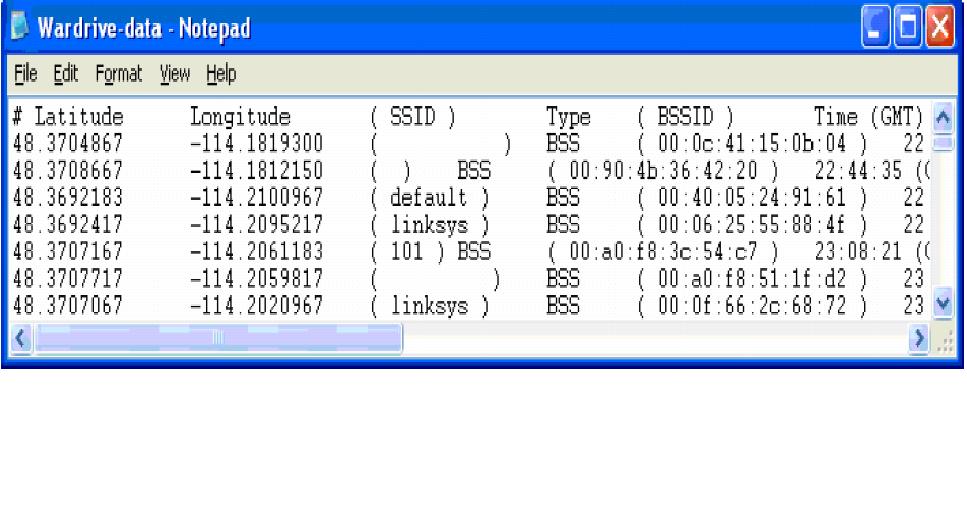
More informationIn this video we will demonstrate how to crack WPA2 using the Airmon-ng suite. We will do it by:
- Identifying an access point
- Capturing traffic from that access point
- Attempt to capture the handshake. We have two options for doing this.
- We can wait for a client to connect on their own
- We can run a deauth attack to force them to disconnect and then you can capture the handshake then
.
Once you have captured the handshake, you can attempt to crack it with a word list or a rainbow table. The key can then be found from there.
Enjoy.